Category: Tech

Jamf Protect Telemetry: Your Mac Fleet’s Security Visibility Engine
If you’re running Jamf Protect, you’re already blocking threats across your Mac fleet. But are you truly understanding what’s happening in your environment? That’s exactly the gap that Jamf Protect Telemetry is designed to fill. In this post, I’ll walk you through what Telemetry is, what it can do for your organization, and how to…

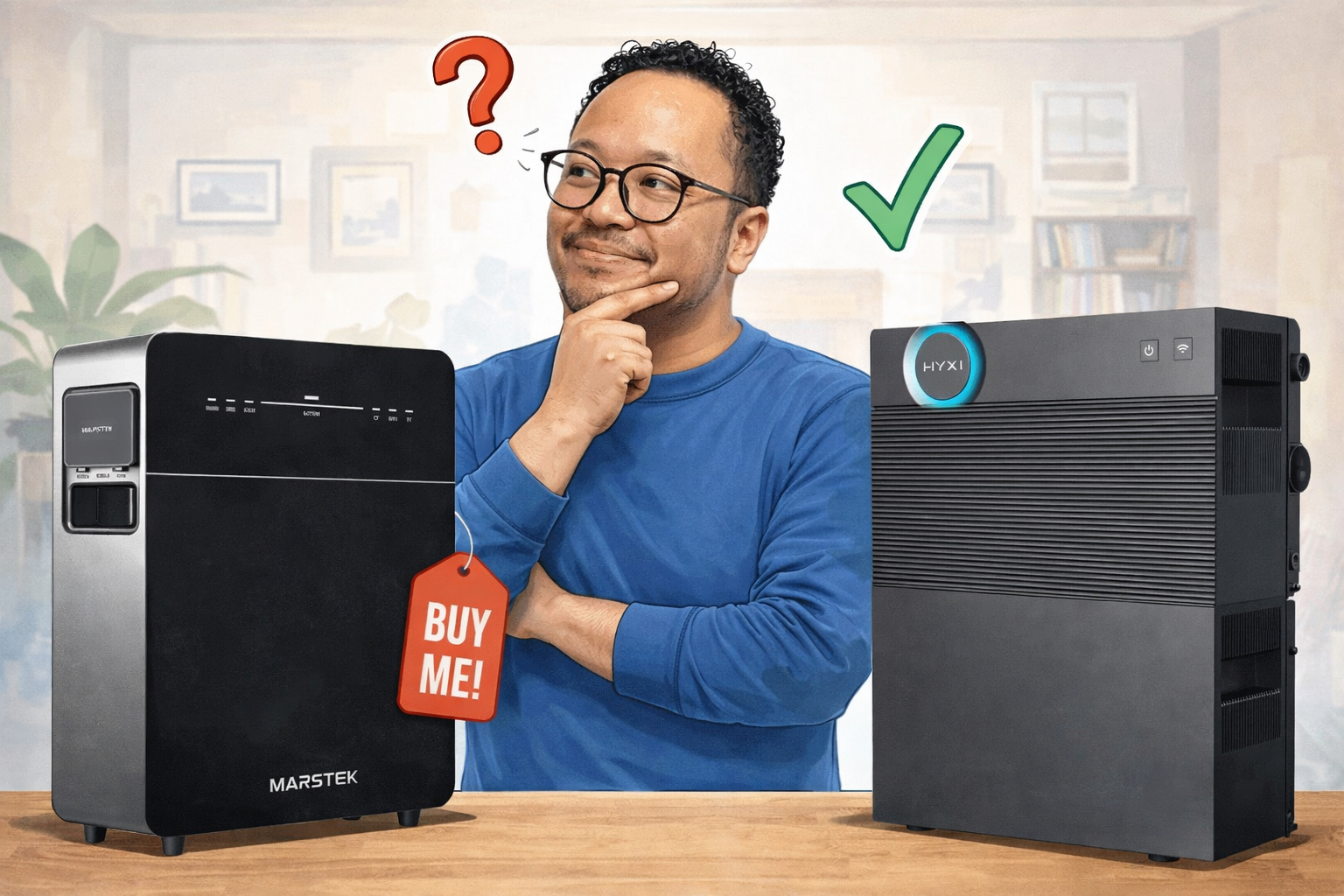
A New Contender: The Hyxi Halo and How It Compares to the Marstek Venus 3.0
Just when I thought my research was done, the Hyxi Halo entered the picture. Here is why it deserves serious attention and how it stacks up against my original choice. A Quick Recap In my previous blog post, I shared the research behind my search for a plug-in home battery. I looked at five models,…

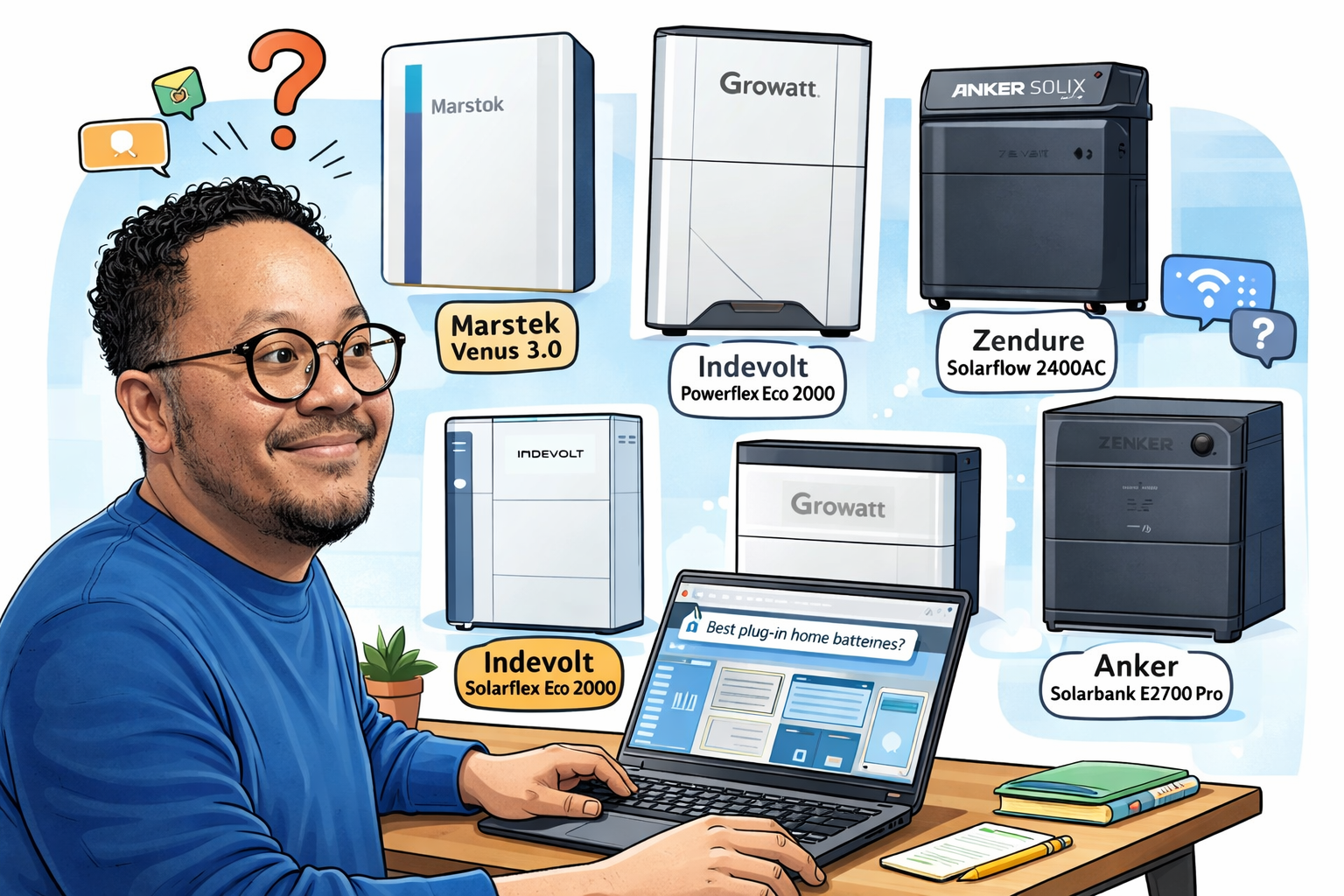
Plug-In Home Batteries: My Research and Why I Am Choosing the Marstek Venus 3.0
A practical guide to five leading plug-in home batteries, comparing specs, P1 meter support, dedicated group capacity, and price per kWh. Why I Started Looking at Plug-In Home Batteries Energy independence has been on my radar for a while. With solar panels already on the roof and a dynamic energy contract, the logical next step…

Why Setting Up Jamf Account SSO Is Important for Your Organization
If you’re managing Apple devices across your organization with Jamf, you’ve likely encountered the challenge of juggling multiple logins across different Jamf products. Jamf Pro, Jamf Protect, etc. each potentially requiring separate credentials. This isn’t just inconvenient. It’s a security risk and an administrative headache. Enter Jamf Account SSO: an authentication solution that transforms how…

Understanding Phishing and Malware: A Simple Guide
In today’s digital world, staying safe online can feel overwhelming, especially if technology isn’t your forte. You don’t need to be a computer expert to protect yourself from cyber threats. This guide is written specifically for everyday people who want to understand the most common dangers lurking on the internet without getting lost in technical…

Understanding Jamf Trusted Access: Your Digital Security Guard
If you’ve ever traveled through an airport, you know the drill: show your ID, scan your boarding pass, walk through security, and only then do you get to your gate. Nobody just wanders onto a plane. There’s a system in place to make sure only the right people get access to the right places. Jamf…

Platform SSO Revisited: The Future of Enterprise Mac Authentication
All credits for the information in this recap that I made, go to Joel Rennich, who presented this topic at MacSysAdmin 2025 in Sweden. This recap is based on his presentation during this event. Why this recap? Because it’s currently a much-discussed topic in the Macadmins space. Platform SSO continues to evolve as Apple’s vision…

EV Experience 2025: A Weekend of Electric Enthusiasm, Connection, and Discovery
Last week’s EV Experience was nothing short of extraordinary. Representing Vereniging Elektrische Rijders (the Dutch Electric Drivers Association) over two inspiring days, I left the event energized, both literally and figuratively, by the passion and curiosity of everyone involved. A Hub for Electric Mobility Conversations The atmosphere at EV Experience was electric in every sense…

October: Cybersecurity Awareness Month. Why It Matters to You and Me
We are entering autumn and It’s also Cybersecurity Awareness Month (CSAM), a time when tech enthusiasts, professionals, and everyday users like you and me come together to sharpen our digital defenses. For those of us in EMEIA (Europe, Middle East, India, and Africa), and indeed around the world, this month is a reminder that cybersecurity…

CIS Level 1 vs Level 2: Complete Guide to Choosing the Right Security Framework
With cyber threats reaching unprecedented levels and data breaches affecting millions of organizations worldwide, implementing robust security frameworks has never been more critical. The Center for Internet Security (CIS) provides two distinct benchmark levels to help organizations protect their IT infrastructure; but which one is right for your business? This blog is a follow-up to…